Nmap is a network scanning tool. By sending packets to the target and analysing the responses, Nmap discovers hosts and the services that are offered. When performing a remote attack, Nmap is useful to discover the open ports in the target.
In command line, by typing in nmap we will see the available commands we can run and what they do. The command we will try to execute is: nmap -sV <target>
The command -sV is used to probe the open ports in the target and determine the service.
The screenshot below shows the result of nmap -sV 128.199.101.40
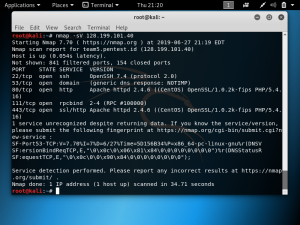
This Nmap scan was done on the IP address and as seen in the screenshot, it led to the domain team5.pentest.id and mentions that the host is up. It reported back the number of closed ports, filtered ports, and the details on the opened ports including the service for each opened port.